Across the European Union, a new wave of cybersecurity enforcement is underway. The NIS2 Directive, the successor to the original Network and Information Security Directive, has dramatically expanded the scope of mandatory requirements, pulling thousands of organizations into compliance obligations they may not have faced before.
But there’s a trap waiting for organizations that treat NIS2 as a paperwork exercise. The directive is explicitly designed to produce demonstrable, continuous security outcomes, not just documented policies. Organizations that tick boxes without fixing the underlying problems are at risk of both regulatory enforcement and, more critically, real-world breaches.
This guide breaks down what NIS2 actually requires under Article 21, why the threat landscape makes compliance harder than it looks, and what a genuine technical response looks like.

What Is NIS2 and who does it apply to?
The NIS2 Directive (EU 2022/2555) entered into force in January 2023, with EU member states required to transpose it into national law by October 2024. It replaces the original NIS Directive and significantly broadens its reach covering sectors from energy and transport to healthcare, digital infrastructure, and beyond.
Where the original directive focused on a relatively narrow set of operators of essential services, NIS2 distinguishes between essential entities and important entities, bringing mid-size companies in critical sectors under mandatory requirements for the first time. The fines are substantial: up to €10 million or 2% of global turnover for essential entities, and up to €7 million or 1.4% of turnover for important entities.
Who is newly in scope
NIS2 expands coverage to include sectors previously outside scope: waste management, postal services, food production, manufacturing, and digital providers. If your organization operates in the EU and exceeds 50 employees or €10M in annual revenue, verify whether you are now subject to NIS2 obligations.
Article 21: the eight Cybersecurity Obligations
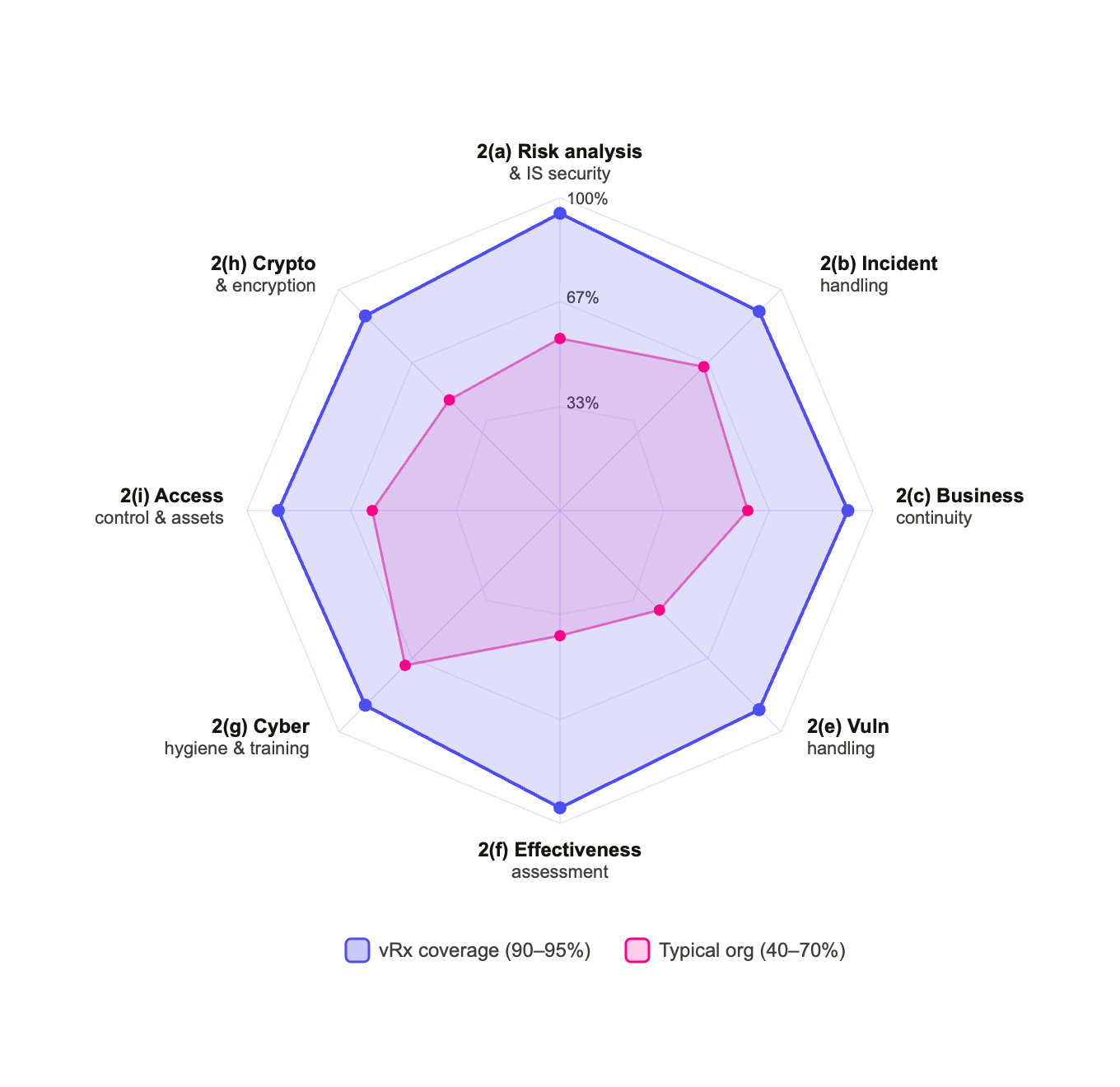
The core technical requirements for NIS2 sit in Chapter IV, Article 21. Organizations must implement “appropriate and proportionate technical, operational and organisational measures” to manage cybersecurity risks. Article 21(2) lists eight specific areas of obligation:

Reading these requirements, two things stand out. First, the scope is comprehensive NIS2 doesn’t pick one or two security domains; it covers the full stack from assets and access control through incident response and effectiveness measurement. Second, the word “demonstrable” matters organizations will need audit-ready evidence, not just internal assertions.
Why NIS2 is harder to meet than it looks
The challenge isn’t understanding what NIS2 requires. The challenge is that the threat landscape has evolved in ways that make traditional security approaches structurally inadequate.
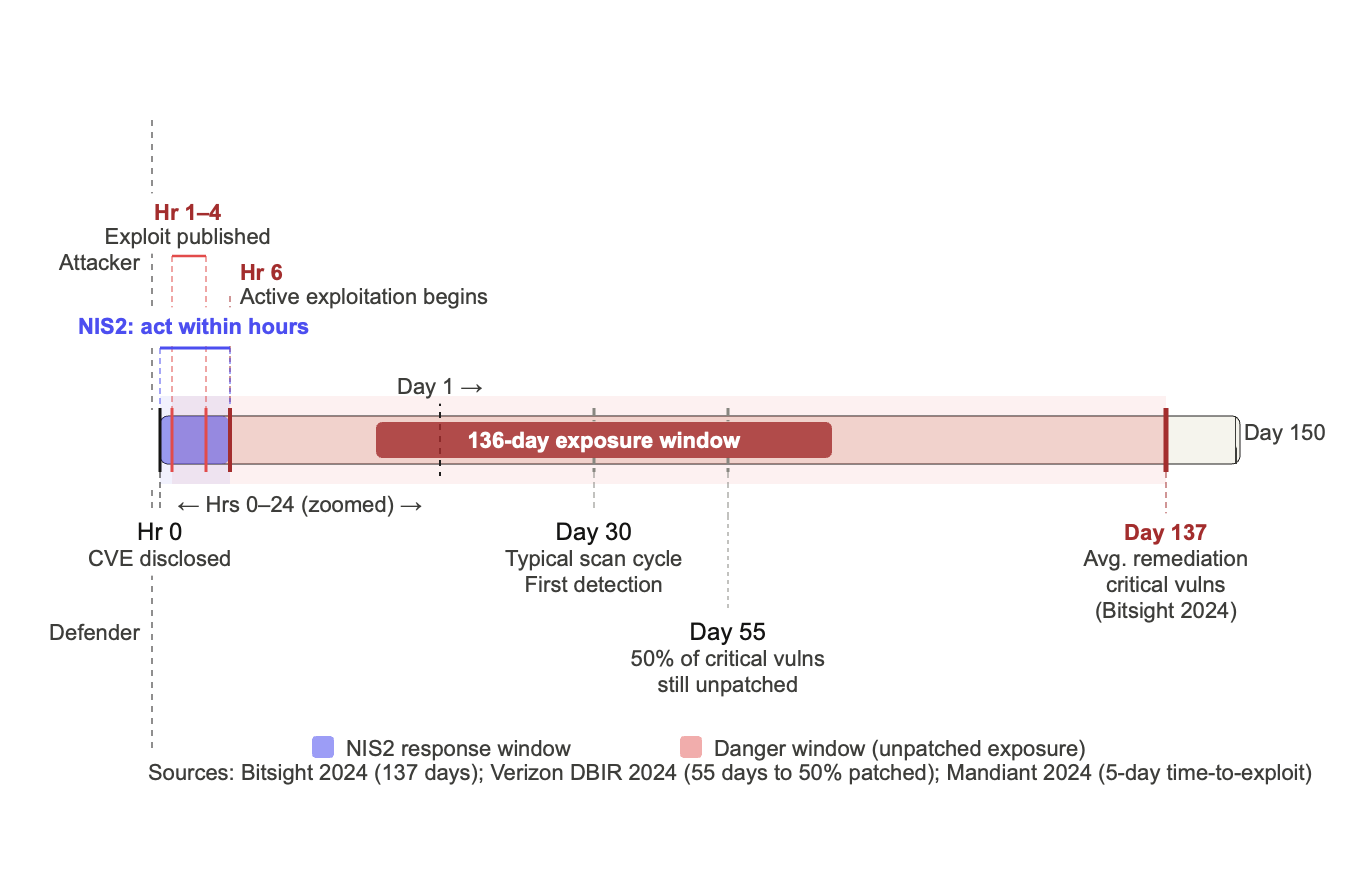
The speed crisis
Most organizations run vulnerability scans monthly. Attackers exploit disclosed vulnerabilities within hours. That gap days or weeks of exposure between discovery and remediation is exactly what NIS2’s incident handling and risk management obligations are designed to close. Monthly scanning cycles cannot produce the continuous visibility Article 21(2)(a) demands.
The accuracy crisis
Traditional vulnerability tools generate enormous volumes of alerts. Industry estimates suggest that over 95% of these are false positives vulnerabilities that are technically present but not exploitable in a given environment. When security teams spend most of their time chasing non-issues, they cannot meet NIS2’s requirement to focus resources on genuine risk.
The remediation crisis
Detection without a validated path to fix is compliance theater. Most platforms stop at identification. Without a closed-loop workflow from discovery through verified fix, roughly 70% of security team time gets absorbed by triage rather than actual remediation. NIS2’s Article 21(2)(f) explicitly requires organizations to assess the effectiveness of their risk-management measures which means proving that fixes actually worked.
The structural blind spot
80% of exploits are published before a CVE is formally assigned. This means organizations relying solely on CVE-based scanning carry a structural 23-day blind spot during the most dangerous window of any vulnerability’s lifecycle.
The incident reporting timeline
NIS2 introduces strict incident notification timelines an early warning within 24 hours of becoming aware of a significant incident, and a detailed report within 72 hours. Meeting these timelines demands real-time asset visibility and pre-built reporting workflows that many organizations currently lack.
The case for closed-loop Remediation
NIS2 compliance isn’t a reporting problem it’s a security operations problem. The organizations that will meet Article 21 requirements most effectively are those that can demonstrate continuous, validated security outcomes across their entire attack surface.
The operational model that maps most directly to NIS2’s requirements follows a closed-loop workflow:

Each step maps to one or more Article 21 obligations. Detection and analysis map to Article 21(2)(a). Validation and rapid response map to 21(2)(b). Re-validation and effectiveness measurement map to 21(2)(f). Without all six steps operating continuously, organizations have compliance gaps they may not discover until an audit or an incident.
Why re-validation is non-negotiable
Post-fix re-validation confirming that a remediation actually resolved the vulnerability rather than simply closing a ticket is often treated as a nice-to-have. Under NIS2, it becomes a requirement. Article 21(2)(f) asks organizations to “assess the effectiveness of cybersecurity risk-management measures.” Without re-validation, that assessment has no technical basis. An audit trail of closed tickets is not the same as an audit trail of confirmed fixes.
Asset visibility: the foundation everything else requires
You cannot manage risk across assets you don’t know exist. Most enterprises have significant blind spots cloud workloads spun up by development teams, containers with no inventory entry, legacy systems running software that hasn’t been formally tracked in years.
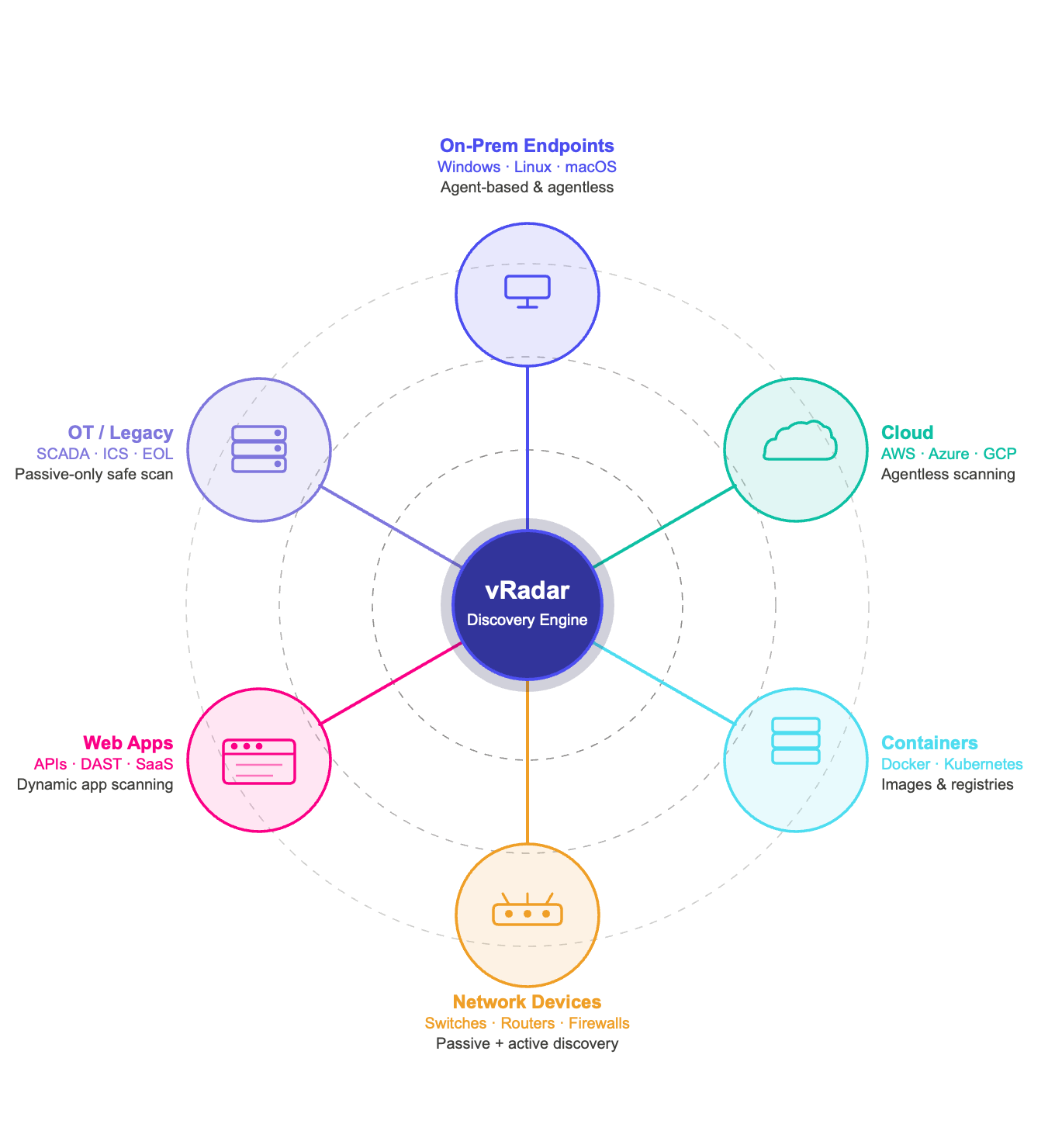
Article 21(2)(i)’s asset management obligation reflects this directly. Organizations need a continuously updated asset register covering software, hardware, SBOM components, and network devices. Effective asset discovery for NIS2 combines:
- Agent-based scanning deep endpoint visibility on managed assets
- Agentless scanning for network devices and systems that can’t run agents
- Passive discovery to catch assets making network traffic without active scanning
- Cloud and container scanning for dynamic infrastructure that traditional tools miss
- Web application scanning for internet-facing attack surface
Smarter prioritization: not all vulnerabilities are equal
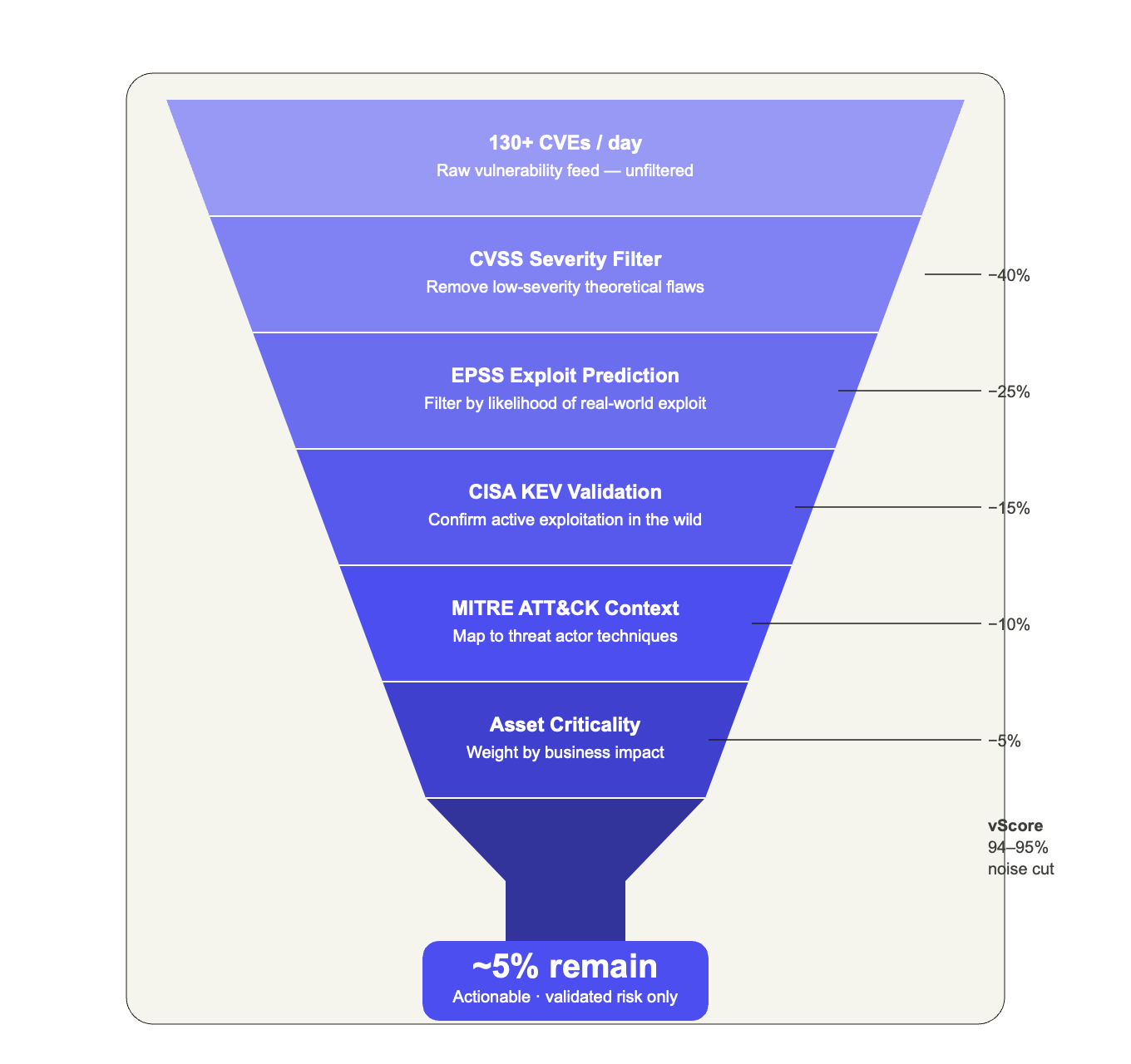
With 130+ new CVEs published daily, prioritization is not optional it’s existential. Effective NIS2-aligned prioritization goes beyond CVSS scores alone. CVSS measures theoretical severity; what NIS2 requires organizations to manage is actual risk in their specific environment.
Modern risk engines address this by fusing multiple signals:
- CVSS base severity score
- EPSS exploit prediction scoring (likelihood of exploitation in the wild)
- CISA KEV confirmed known exploited vulnerabilities requiring immediate attention
- MITRE ATT&CK context mapping vulnerabilities to active threat actor techniques
- Asset criticality weighting by the business importance of the affected system
- Customer-generated context site-specific factors only your team knows
This kind of contextual risk scoring can reduce the actionable vulnerability set by 94–95%, cutting through the noise to surface vulnerabilities that genuinely warrant immediate attention.
Agentic AI validation: proof before you patch
Even after intelligent prioritization, security teams face a persistent challenge: not every high-risk vulnerability is actually exploitable in a specific production environment. Sending patch teams to fix vulnerabilities that can’t be triggered wastes remediation cycles and can cause unnecessary system disruption.
Agentic AI validation addresses this by running exploit validation against actual systems without disrupting production to confirm whether a vulnerability is genuinely exploitable in that specific configuration. This delivers two benefits that directly support NIS2 compliance:
1. Accuracy Remediation resources go to vulnerabilities confirmed exploitable, not theoretically possible
2. Evidence The validation result produces an audit trail supporting Article 21(2)(f)’s effectiveness assessment requirement
What good looks like for NIS2 auditors
An auditor reviewing your NIS2 compliance wants to see a documented chain from vulnerability discovery through risk scoring, exploit validation, remediation execution, and post-fix confirmation. Each step should produce a timestamped, exportable record. The more automated this chain is, the more consistently it can be reproduced across thousands of assets.
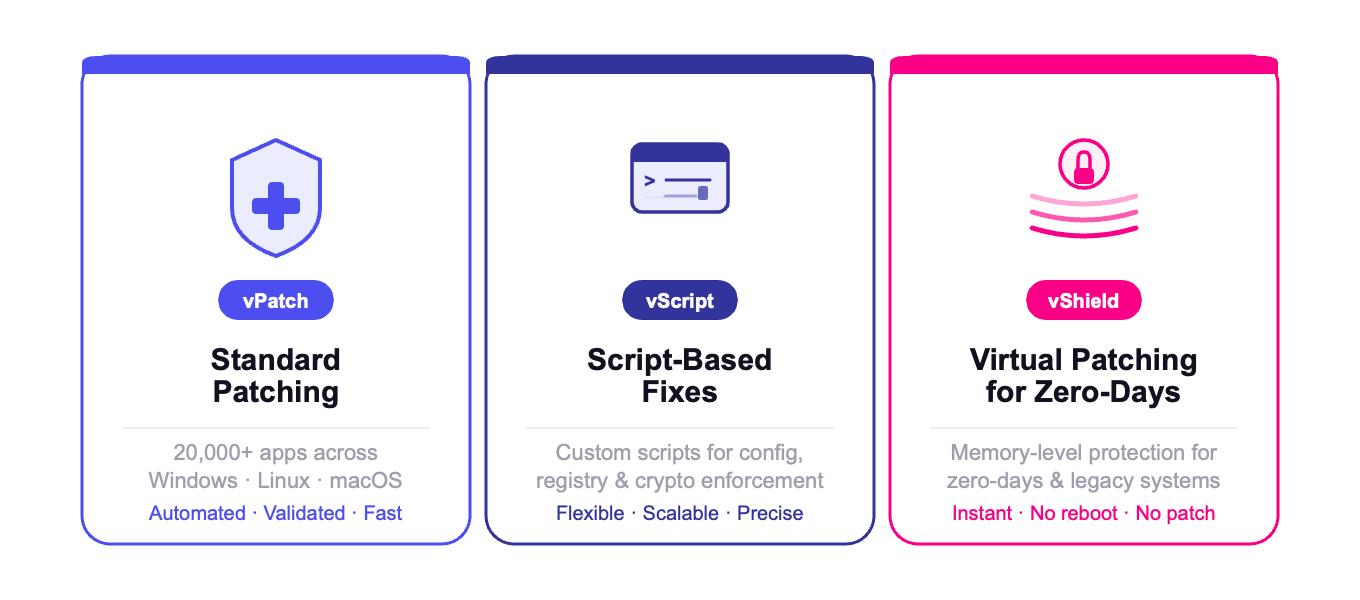
Three Remediation methods for every scenario
A common gap in vulnerability management programs is coverage tools that handle standard patching well but struggle with Linux endpoints, legacy systems, or zero-days for which no vendor patch exists. NIS2’s Article 21(2)(e) covers the full vulnerability handling lifecycle.
1. Standard Patching (vPatch)
For the majority of vulnerabilities, automated patch deployment is the fastest path to remediation. This needs to work across operating systems (Windows, Linux, macOS) and cover the full third-party software inventory not just OS-level patches across 20,000+ applications.
2. Script-based Remediation (vScript)
Some vulnerabilities require configuration changes, registry edits, or custom fixes rather than traditional patching. Script-based remediation handles these cases at scale, including enforcement of cryptographic policy configurations required under Article 21(2)(h).
3. Virtual Patching / memory-level mitigation (vShield)
For zero-days, legacy systems that cannot be taken offline, and high-availability systems where emergency patching would cause unacceptable downtime, memory-level mitigating controls provide immediate protection without disrupting operations. Directly relevant to Article 21(2)(c)’s business continuity requirements.
Building the audit-ready evidence chain
Every obligation in Article 21 implies an evidence requirement. When NIS2 supervisory authorities conduct assessments, organizations need to produce documentation demonstrating continuous, effective security practices not just point-in-time snapshots.
The compliance reporting layer needs to cover:
- CIS benchmark compliance 100+ benchmarks with continuous assessment against hygiene standards
- MTTR metrics mean time to remediate by severity, SLA adherence, and exposure window tracking
- Remediation effectiveness post-fix re-validation rates and confirmed closure rates
- Risk posture over time trending data showing whether the program is improving
- Framework mapping alignment with NIST CSF 2.0, CIS Controls v8, and ISO/IEC 27001

Key takeaways: what NIS2 requires in practice
For organizations working toward NIS2 compliance, here is what the technical implementation picture needs to include:
- Continuous asset discovery across network, cloud, container, and web application assets not quarterly snapshots
- Contextual risk prioritization that fuses CVSS, EPSS, KEV, and asset-specific factors to cut through alert noise
- Closed-loop remediation that moves from detection through validated fix in a single, auditable workflow
- Post-fix re-validation confirming that every remediation actually worked not just closed a ticket
- Coverage for every vulnerability type: patching, scripted fixes, and virtual patching for zero-days and legacy systems
- Exportable compliance reports aligned to Article 21’s specific requirements and major security frameworks
- Access control and identity governance with automatic deprovisioning when employees leave
- Documented cybersecurity training covering vulnerability identification, prioritization, and remediation
The organizations that will navigate NIS2 enforcement most effectively are not those with the most elaborate compliance documentation. They are those that have built operational security programs that continuously discover, prioritize, remediate, and verify and can prove it.
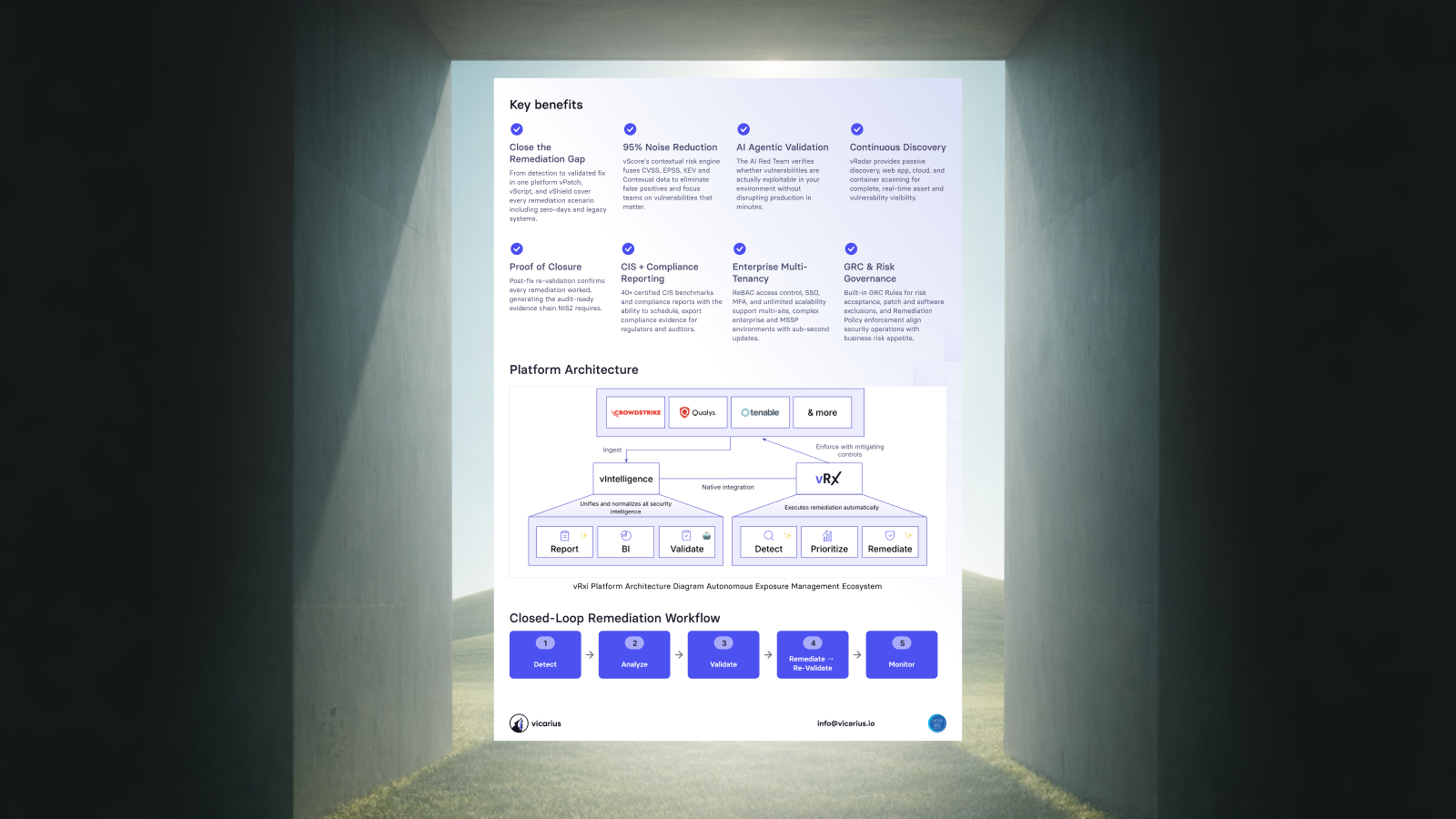
See how Vicarius vRx maps to NIS2 article 21
vRx is the first platform to close the entire remediation gap from multi-vendor intelligence ingestion through agentic AI validation to automated, re-validated remediation with proof of closure.
Disclaimer: The information in this article does not constitute legal advice. The use of Vicarius products alone does not guarantee legal compliance. Organizations are solely responsible for compliance with all applicable laws and regulations and should consult their own legal counsel.