The cybersecurity industry is harboring a dirty secret that most vendors refuse to openly acknowledge: we are exceptionally good at finding vulnerabilities, yet remarkably terrible at actually fixing them. For CISOs, CTOs, and VPs of Engineering, this uncomfortable reality plays out daily across complex enterprise environments.
Security teams possess an arsenal of sophisticated scanners and detection mechanisms that can identify a flaw in seconds, but fully deploying the necessary patch often takes months. This growing disparity between discovery and resolution has transformed a manageable remediation gap into a full-blown crisis, leaving critical infrastructure exposed while engineering teams drown in insurmountable ticketing queues.
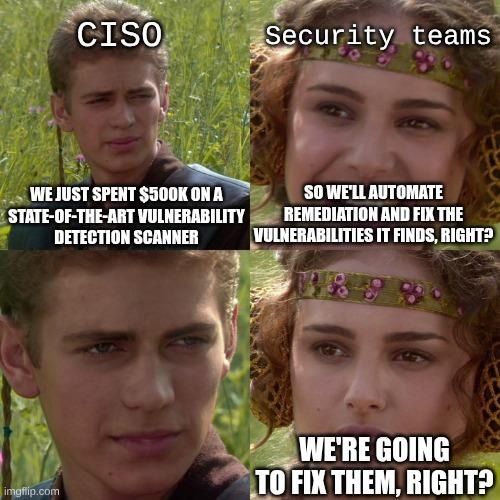
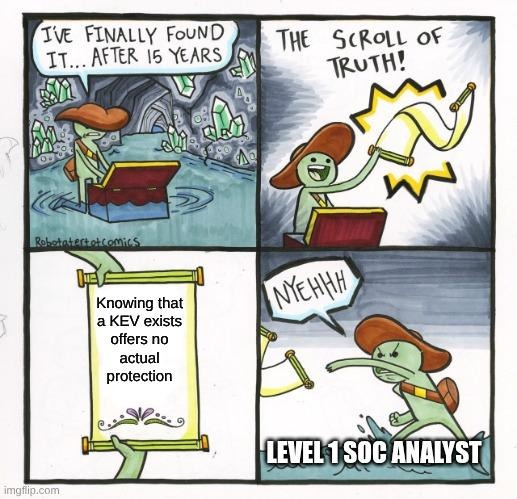
To understand the severity of this issue, one must examine where security budgets are predominantly allocated. Organizations spend millions annually on cutting-edge detection platforms, threat intelligence, and continuous monitoring tools. However, merely knowing that a vulnerability exists offers absolutely zero tangible protection. Without a reliable, immediate path to deployment, a detected exposure is nothing more than a liability sitting in a dashboard.
Remediation delays vs. threat velocity: Bringing the receipts
This imbalance means that despite massive investments in visibility, enterprise infrastructure remains dangerously vulnerable to exploitation simply because the most critical step, remediation, is often treated as an operational afterthought. The severe delays in enterprise patching are no longer anecdotal; they are backed by alarming industry data.
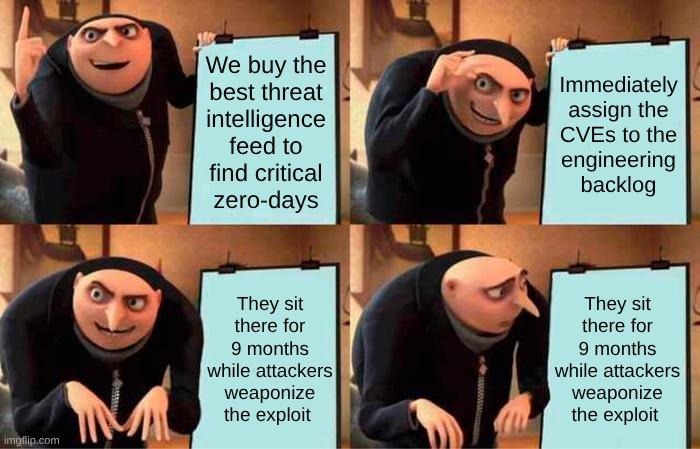
Currently, the average time to remediate a vulnerability has ballooned to an astonishing 270 days. This means that after a security flaw is identified and logged, it typically languishes for up to nine months before a fix is successfully implemented across the network. Such an extensive delay provides threat actors with an incredibly wide window of opportunity, completely undermining the value of rapid detection and leaving systems practically defenseless against active campaigns.
This prolonged exposure is especially dangerous given the aggressive velocity and sophistication of modern threat actors. Attackers no longer wait for the security community to casually roll out patches. In fact, nearly 29% of known exploited vulnerabilities are weaponized on or before the day their Common Vulnerabilities and Exposures (CVE) identifier is published, often before the vulnerability even appears on the Known Exploited Vulnerabilities (KEV) alert list. This stark reality renders reactive, manual patching strategies obsolete, as a significant portion of the attack surface is actively being targeted before defenders even have a chance to assess the formal documentation or formulate a response plan.
The risk becomes even more pronounced when examining mission-critical infrastructure and high-priority alerts. Shockingly, even critical severity vulnerabilities can take an average of 65 days to remediate. For decision-makers, this metric should be deeply concerning; it implies that known, critical flaws - those with the highest potential to cause business catastrophe - are routinely left exposed to the open internet for multiple months before the vulnerability is finally closed.
The required shift toward continuous, automated remediation
The cybersecurity industry requires an immediate paradigm shift away from reactive, manual patching processes. To truly secure modern infrastructure against rapidly weaponized exploits, organizations must transition toward continuous, automated, and intelligence-driven remediation workflows. This approach entirely eliminates the dangerous gap between detection and action, transforming vulnerability management from a passive reporting exercise into a proactive, outcome-driven defense mechanism.
Mitigating risks at the speed of modern threats through automation
Automating the remediation lifecycle is the only viable way for organizations to seamlessly push fixes and neutralize vulnerabilities as fast as they are discovered. By integrating automation into the patching pipeline, security and engineering teams can replace slow, error-prone manual deployments with streamlined execution that matches the velocity of today's attackers.
Adopting an automated framework provides several advantages:
- Accelerated response times: Automation ensures that patches are deployed instantly upon discovery and approval, neutralizing threats before they can be exploited.
- Reduced human error: Removing manual intervention prevents critical updates from being overlooked, delayed, or improperly configured during complex rollouts.
- Optimized resource allocation: Security and IT professionals can reclaim countless hours previously lost to manual ticket chasing, redirecting their focus toward higher-level strategic initiatives.
Securing unpatchable assets with patchless protection
A critical component of this modern remediation capability is "patchless protection," also known as in-memory protection. This technology provides immediate risk mitigation for legacy systems, zero-day threats, or critical operational assets that simply cannot be taken offline for a hard patch without causing unacceptable business disruption. By securing the vulnerability directly in memory without altering the underlying source code or requiring a system reboot, patchless protection offers a highly effective compensating control. It keeps essential services running smoothly while decisively neutralizing the threat until a permanent patch can be safely scheduled and applied.
Prioritizing actionable remediation over alert generation
Ultimately, the value of a security program must be measured by its ability to resolve issues, not merely report them. Prioritizing actionable remediation over the generation of more alerts is essential because fixing the problem is what truly matters to the business's bottom line and risk posture. An endless stream of vulnerability reports is virtually useless - and often actively counterproductive - if it does not directly feed into a workflow capable of immediately closing the loop on the exposure. By shifting the organizational focus from discovery to deployment, teams can finally break free from alert fatigue and achieve measurable, resilient security outcomes.
Operational bottlenecks and cultural silos are hindering remediation
The foundational flaws of legacy vulnerability management are rooted in traditional "find and fix" workflows that rely entirely on rigid CVE identifiers, KEV alerts, and endless manual ticketing queues. These antiquated systems were designed for simpler, on-premises networks and are fundamentally incapable of keeping pace with the dynamic nature of modern cloud and containerized environments. As digital footprints expand, these rigid workflows buckle under the sheer volume of vulnerabilities, leading to insurmountable backlogs and operational paralysis.
This structural failure is further exacerbated by the cultural and operational friction between the teams responsible for security and those responsible for engineering. Security teams operate with a mandate to generate alerts and highlight risks, while Engineering and IT teams are tasked with the delicate, manual work of patching without disrupting system uptime.
This siloed approach inherently delays time-to-remediation due to several recurring conflicts:
- Misaligned performance metrics: Security is measured by risks found, whereas IT is measured by system availability, creating a natural hesitancy to deploy potentially disruptive patches.
- Communication breakdowns: Tickets are often tossed over the wall with little context, leaving IT struggling to understand the operational impact or urgency of the fix.
- Duplication of effort: Both teams frequently use entirely different tools to track the same vulnerability, leading to fragmented visibility and prolonged debates over ownership.
Consequently, teams inevitably suffer from severe alert fatigue. Relying on raw Common Vulnerability Scoring System (CVSS) scores without contextual, risk-based prioritization leads organizations to waste critical time and resources patching low-risk assets. When every alert is flagged as a high priority, nothing is truly a priority, causing genuinely critical, internet-facing vulnerabilities to go ignored while engineers chase low-impact flaws simply to clear the queue.
Enabling continuous action with vRx by Vicarius
To overcome these systemic failures, organizations require a solution built specifically for action. While many platforms focus heavily on detection or prioritization, vRx by Vicarius is purpose-built to lead and address the most critical part of the vulnerability lifecycle: remediation. By prioritizing the actual deployment of fixes over generic management, the platform ensures that identified risks are decisively neutralized rather than endlessly debated in a ticketing system.
A core component of this strategy is the "Better Together" approach, which recognizes that organizations already rely on a variety of scanners and security tools. vRx expands its integrations to plug seamlessly into any detection tool an organization is already using. This collaborative ecosystem helps teams bridge the operational divide, allowing them to smoothly transition from "now we know" to "now it's fixed" without disrupting their existing security investments.
Underpinning this capability is proprietary, automation-first technology designed to streamline and execute continuous remediation. vRx avoids making inflated claims about being a mythical "single pane of glass," instead focusing purely on the practical outcome of fixing exposures regardless of where they were originally detected. By concentrating strictly on actionable risk mitigation, vRx delivers tangible security improvements through rapid, reliable, and continuous remediation.
Continuous action: The future of vulnerability management
The widening gap between vulnerability discovery and effective patching has escalated into an undeniable crisis for enterprise security. With the average remediation time stretching to 270 days and threat actors routinely weaponizing exploits on day zero, traditional, manual workflows are proving to be critically insufficient. If organizations hope to survive the aggressive and fast-paced modern threat landscape, vulnerability management must evolve from a passive exercise in generating alerts into a unified system of continuous action. Embracing automated patching, adopting patchless protection for unpatchable assets, and breaking down the operational silos between security and IT are no longer optional strategies. True security maturity requires a fundamental shift in focus: knowing about a problem is just the beginning, but seamlessly and rapidly fixing it is the only way to genuinely protect the business.
It is time to stop chasing endless remediation queues and start closing the loop on vulnerabilities. IT and Security decision-makers must adopt a unified approach that prioritizes immediate, automated action over perpetual alert fatigue. Discover how you can transform your security posture by learning more about vRx, our purpose-built remediation technology, or request a personal demo today to see continuous, automated remediation in action.