The landscape of software supply chain security has undergone a rapid and perilous transformation, evolving far beyond the days of manual repository poisoning. Today, engineering and security leaders face highly infectious, self-propagating worms capable of tearing through dependencies at unprecedented speeds.
According to recent data, supply chain attacks have quadrupled since 2020, signaling a definitive shift in adversary tactics. For Chief Information Security Officers and Vice Presidents of Engineering, this surge represents not just a higher volume of attacks, but a fundamental change in how malicious code operates, hides, and spreads within enterprise environments. When threats can propagate autonomously across connected ecosystems, detection is only a fraction of the battle; the true measure of enterprise resilience now lies in how rapidly an organization can neutralize the vulnerability before the worm moves laterally.
The compounding risk of interconnected open-source ecosystems
As adversaries increasingly automate their exploits to maximize impact, relying on traditional security postures is no longer tenable. The core reality of this new era is that organizations must aggressively pivot from merely identifying and categorizing exposures to actively taking action and remediating them. Open-source ecosystems serve as the foundational building blocks for virtually all modern enterprise applications, but this deeply interconnected nature uniquely compounds their security risks. When thousands of applications rely on a single nested dependency, a compromise in that deeply buried module instantly creates a massive, distributed blast radius. The modern software supply chain operates on an implicit web of trust, meaning that when a malicious payload enters an upstream package, it effortlessly cascades downstream into secured corporate environments without tripping traditional perimeter alarms.
Historically, supply chain breaches were characterized by isolated, manual interventions where attackers meticulously compromised a specific vendor or repository to reach a predetermined target. This targeted approach was highly effective but inherently slow, requiring significant time and resource investments from threat actors. However, as the digital ecosystem has matured, these threats have made a dangerous transition toward autonomous spreading mechanisms. Today’s supply chain attacks mimic biological viruses, programmed to automatically seek out adjacent vulnerabilities, harvest credentials, and not merely replicate themselves across registries without any further human input, but to also rewrite themselves in ways often dangerously analogous to biological evolution - and with the same unpredictable results.
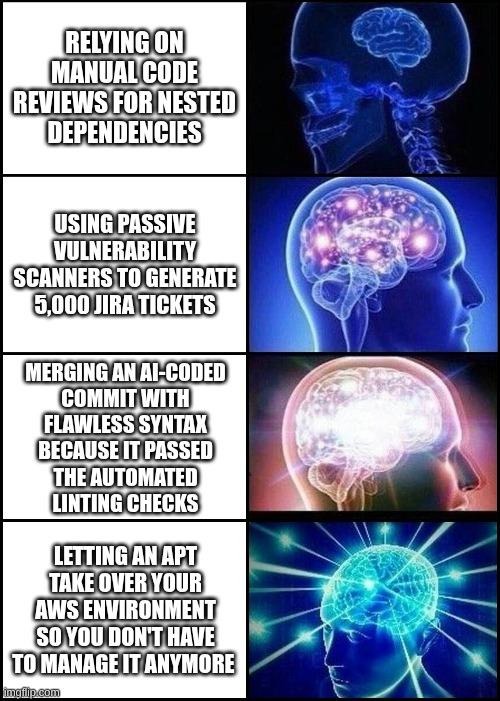
Compounding the danger of these self-propagating threats is the increasingly sophisticated use of artificial intelligence to mask the initial intrusion. Attackers are now using Large Language Models (LLMs) to generate highly convincing "cover commits," effectively camouflaging their malicious code injections within what appear to be legitimate feature updates or bug fixes.
The use of AI in these attacks introduces several critical advantages for threat actors:
- Syntactic perfection: Generating flawlessly formatted code that easily passes automated linting and syntax checks.
- Contextual relevance: Crafting commit messages and pull request descriptions that perfectly match the tone and style of the targeted open-source project.
- Behavioral obfuscation: Distributing malicious payloads across multiple smaller, seemingly innocuous commits to avoid triggering manual review alarms.
Deconstructing the lifecycle of an autonomous supply chain pathogen
The comprehensive anatomy of a modern supply chain attack begins not with a direct assault on the enterprise perimeter, but with a calculated breach deep within the open-source ecosystem. Understanding this lifecycle is critical for engineering and security leaders, as these threats no longer rely on manual execution but instead operate as autonomous pathogens. By deconstructing how these worms breach, spread, and exploit, organizations can better identify the critical junctures where active remediation must replace passive detection.
The initial breach: Establishing patient zero
The modern supply chain worm originates with a strategic compromise of a trusted open-source package, which serves as the infection's patient zero. Adversaries target overworked maintainers, exploit abandoned projects, or leverage compromised developer credentials to quietly introduce their initial payload into a widely used repository. Once this infected package is downloaded and integrated into downstream CI/CD pipelines, the malicious code activates, effectively bypassing internal enterprise defenses by riding in on the coattails of legitimate, trusted software updates.
Autonomous propagation: The CanisterWorm case study
The true danger of these modern threats lies in their autonomous propagation mechanisms, which require zero human oversight once deployed. A prime example is the 2026 CanisterWorm, which demonstrated a frightening capacity for self-replication. Once introduced into the ecosystem, the CanisterWorm spread across 47 individual npm packages autonomously by scanning for adjacent repositories, injecting its malicious payload, and pushing new, infected versions back to the registry using harvested maintainer tokens.
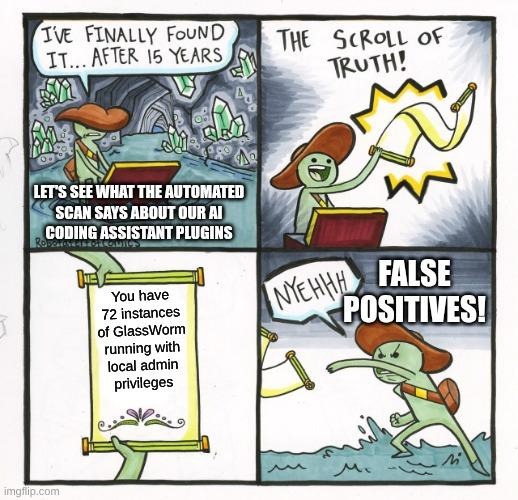
Targeting developer ecosystems: The GlassWorm threat
Threat actors are increasingly aiming their automated payloads directly at the tools developers use every day, recognizing that compromising the local development environment provides unparalleled, highly privileged access. This deliberate targeting was starkly evident when GlassWorm successfully infected 72 Open VSX extensions specifically aimed at AI coding assistants. By embedding malicious logic directly into the plugins that engineers rely on for code generation and optimization, attackers ensured their malware was executed on local workstations, effectively “poisoning the water before it reaches the well” - subverting the supply chain before the code ever reached a formal enterprise repository.
High-velocity exploitation: UNC6426 and the 72-hour window
Once a foothold is established, the frightening speed of the exploitation phase leaves security teams with an impossibly brief window for response. This extreme velocity was demonstrated when the UNC6426 threat group leveraged a single npm breach to secure comprehensive AWS administrator access in under 72 hours. Moving laterally from the initial compromised package, the attackers rapidly scraped environment variables, escalated privileges, and established persistent cloud access long before traditional security alerts could be properly triaged.
Strategic challenges for engineering and security leaders
For CTOs and CISOs, this rapid infection cycle poses immense strategic and operational challenges. Traditional detection-only cycles simply cannot outpace self-propagating worms that compromise and pivot within minutes. Relying on scheduled vulnerability scans, manual code reviews, or lengthy triage meetings creates a critical lag time. During this operational delay, an autonomous pathogen can deeply embed itself into production environments, exfiltrate sensitive data, and replicate further downstream.
The operational reality: Moving beyond detection
The stark operational reality of defending against viral supply chain attacks is that simply knowing about these rapidly spreading vulnerabilities is entirely insufficient. When a worm moves laterally in hours, merely logging a CVE or sending an alert to a dashboard offers no real protection. Organizations require a seamless, automation-first approach to active remediation. To survive this era of automated exploits, security operations must mirror the speed and autonomy of the threats they face, shifting decisively from passive alert generation to immediate, programmatic neutralization.
Concrete mitigations and defenses
To counter the immediacy of these threats, development teams must implement actionable, concrete mitigations, starting with dependency cooldown periods. By enforcing a deliberate delay before newly published package versions can be ingested into corporate build environments, teams mitigate the risk of pulling in freshly compromised code. This buffer window allows the broader security community time to identify and report anomalous behavior or malicious commits, effectively starving a newly deployed worm of immediate corporate targets.
Securing the build pipeline against unauthorized access demands strict token hygiene and the adoption of - and adherence to - modern authentication standards. Implementing OpenID Connect (OIDC) is an absolute necessity, as it allows continuous integration systems to securely authenticate with cloud providers using short-lived, verifiable identity tokens rather than long-lived, static secrets. By eliminating hardcoded credentials that self-propagating worms actively hunt for, organizations can drastically reduce the lateral movement capabilities of an attacker who successfully breaches a developer’s workstation.
Defending your supply chain against sophisticated subversion attempts absolutely requires the strategic integration of diverse security and scanning tools with a unified remediation workflow. Advocating for a "Better Together" approach to enterprise security ensures that organizations are not operating in siloed environments where detection tools fail to communicate with patching mechanisms.
To operationalize this strategy effectively, organizations must focus on key integration principles:
- Unified visibility: Ensuring that data from static analysis, dynamic testing, and software composition analysis flow into a single operational pipeline.
- Automated patching workflows: Connecting detection alerts directly to patching mechanisms to minimize the time to resolution.
- Collaborative security culture: Fostering deep alignment between development and security teams to ensure that fixes are deployed without breaking production builds.
Navigating this complex landscape requires tools designed specifically to bridge the gap between finding a problem and fixing it. vRx by Vicarius is a purpose-built vulnerability remediation platform that directly addresses the speed and scale of viral supply chain attacks. It operationalizes the "Better Together" philosophy by seamlessly integrating with any existing detection or scanning system an organization already uses. By connecting these diverse inputs into a centralized, automation-first engine, vRx empowers security teams to shift away from passive exposure identification and embrace active, automated remediation.
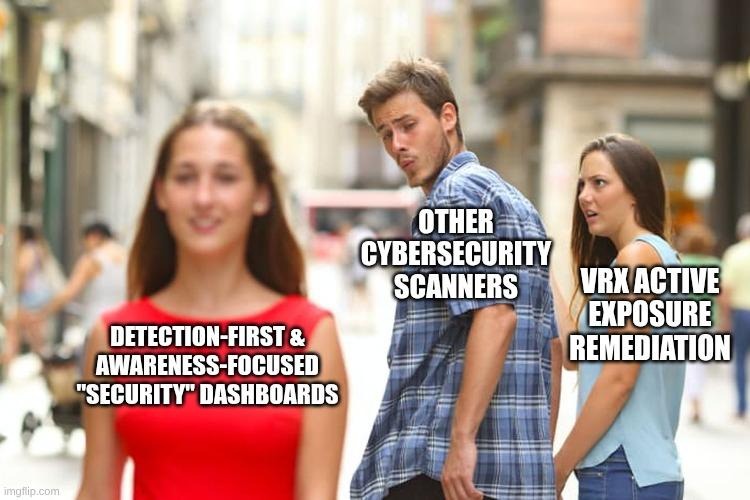
Moving from passive vulnerability management to active remediation
The viral nature of modern supply chain worms necessitates a fundamental shift from passive vulnerability management to aggressive, active exposure remediation. As threat actors continue to weaponize open-source ecosystems with autonomous, AI-camouflaged pathogens, relying on detection alerts and manual patching cycles is a failing strategy. Engineering and security leaders must acknowledge that the velocity of these attacks demands a corresponding velocity in response, moving beyond mere visibility to ensure actual, quantifiable risk reduction.
To achieve this operational agility, organizations need solutions focused entirely on the outcome that matters most. vRx helps organizations fix what matters fast, respecting the complexity of enterprise environments without relying on unnecessarily complex architectures. Embrace an automation-first approach; book a demo today and discover how vRx’s seamless efficiency and integration with your existing tools can help you move your operations from "now we know" to "now it's fixed" - faster and smarter.